![IP SLAs Configuration Guide, Cisco IOS Release 15M&T - Configuring IP SLAs UDP Echo Operations [Cisco IOS 15.4M&T] - Cisco IP SLAs Configuration Guide, Cisco IOS Release 15M&T - Configuring IP SLAs UDP Echo Operations [Cisco IOS 15.4M&T] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/000001-100000/45501-50000/47501-48000/47914.ps/_jcr_content/renditions/47914.jpg)
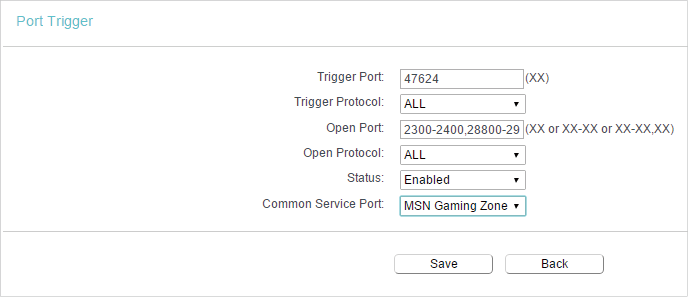
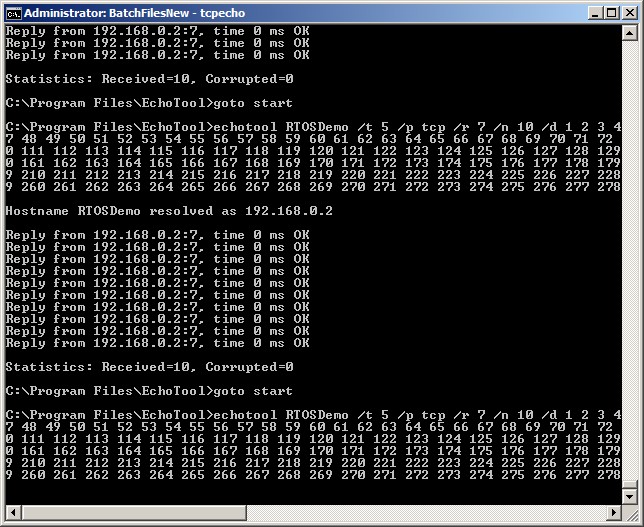
IP SLAs Configuration Guide, Cisco IOS Release 15M&T - Configuring IP SLAs UDP Echo Operations [Cisco IOS 15.4M&T] - Cisco
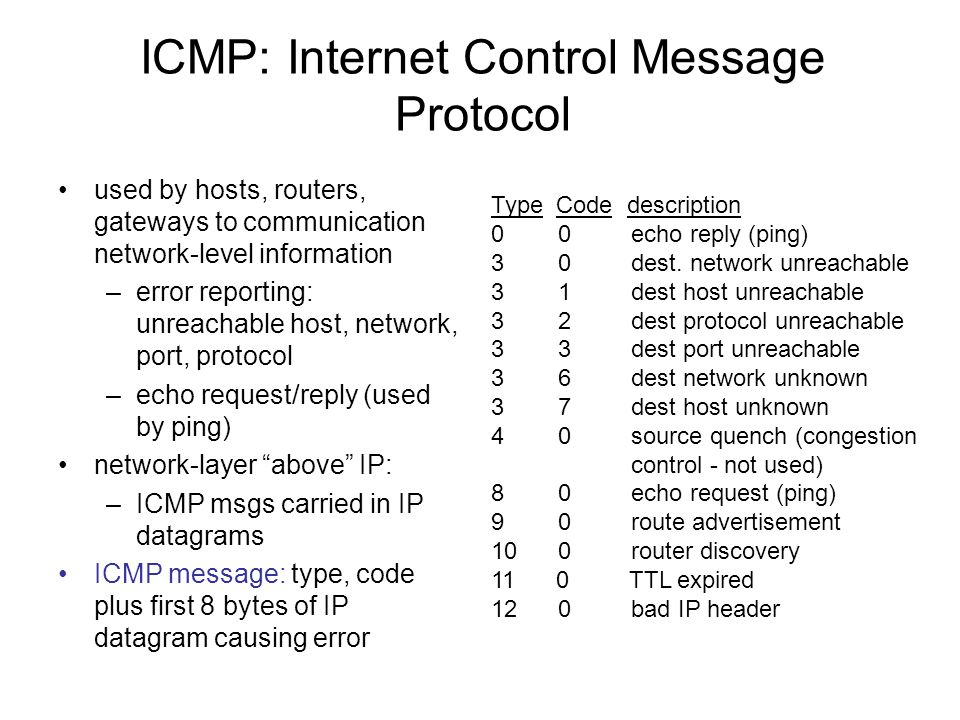
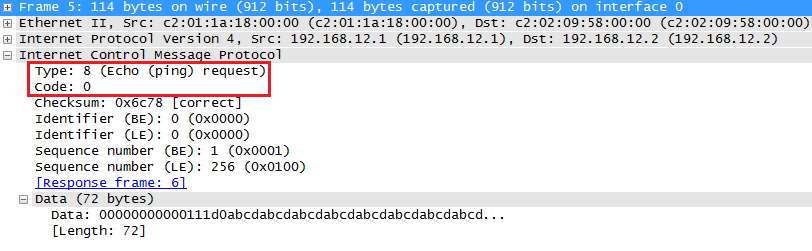
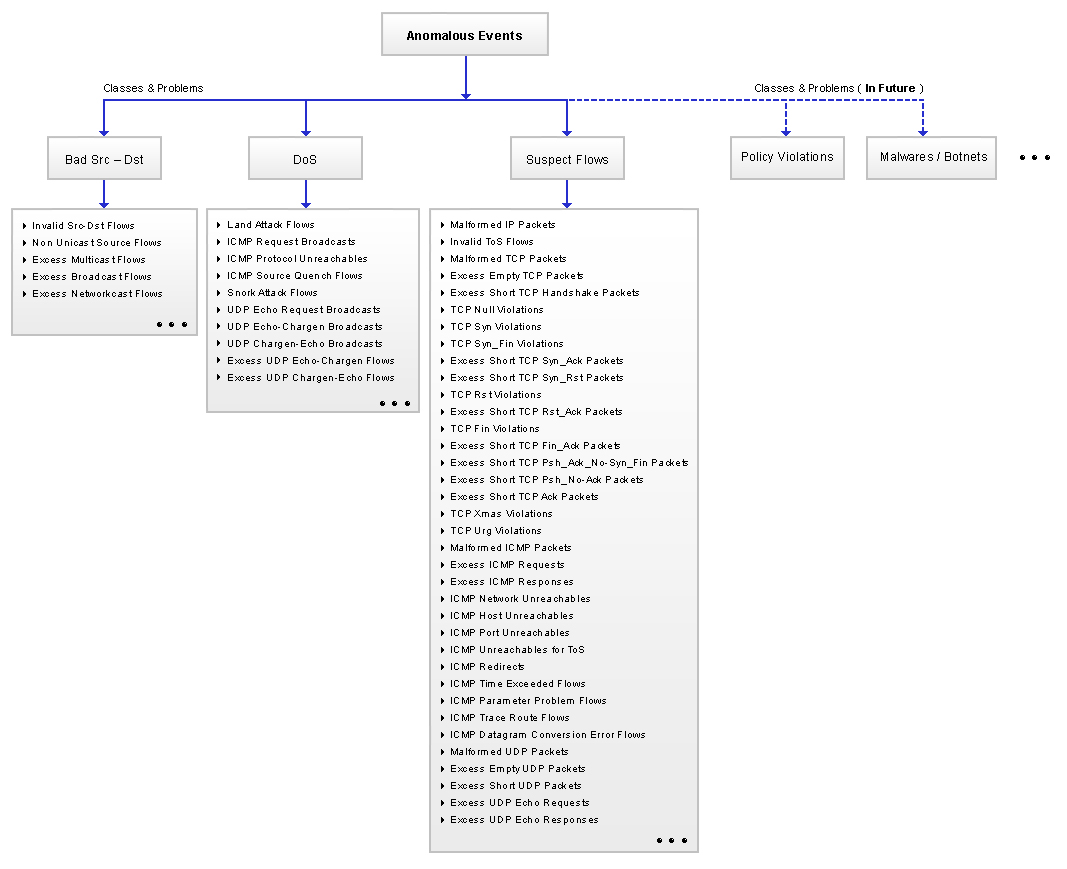
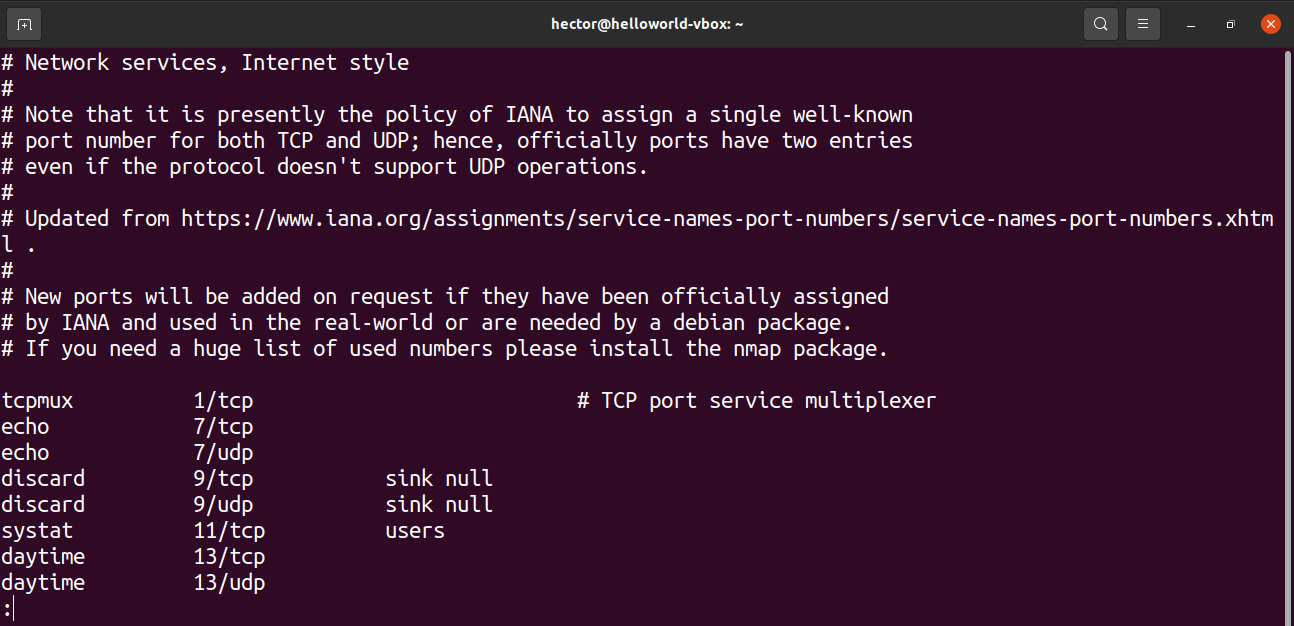
ICMP: Internet Control Message Protocol used by hosts, routers, gateways to communication network-level information –error reporting: unreachable host, - ppt download